Overview of IT Analytics
IT Analytics provides cube based reporting (pivot tables), additional reports, and Key Peformance Indicators (KPIs) for various Symantec products:
- Symantec IT Management Suite (Altiris)
- Symantec Data Loss Prevention (DLP)
- Symantec Critical Systems Protection (CSP)
- Symantec Endpoint Protection (SEP)
IT Analytics is developed by Bay Dynamics but is available as part of your Symantec license. For more information visit: http://baydymanics.com/Products/ITAnalytics/Symantec/
One of the concerns in the past for using IT Analytics has been the requirement for a Symantec Management Platform (SMP also known as Altiris) to be configured first before you install and manage the cubes. This is no loner the case as there is a stand-alone version of IT Analytics available (this will be covered in a separate blog post). This post will cover why you should be using IT Analytics for your DLP system.
Why IT Analytics for Symantec DLP
Within the Symantec DLP console there are a bunch of ways to slice and dice the data that is generated in the system (Incidents, etc.) either by filtering the data or by creating various summarizations of the data. IT Analytics adds several items that are not exposed without having to write a SQL query or leverage the API. IT Analytics allows for someone who does not have access to the DLP console to run reports against the information. Also IT Analytics can easily create trending reports to demonstrate how risk is being reduced over time.
Whenever people ask me why I should bother with IT Analytics there are two reports that I point to that demonstrate the value of IT Analytics.

User Login Report
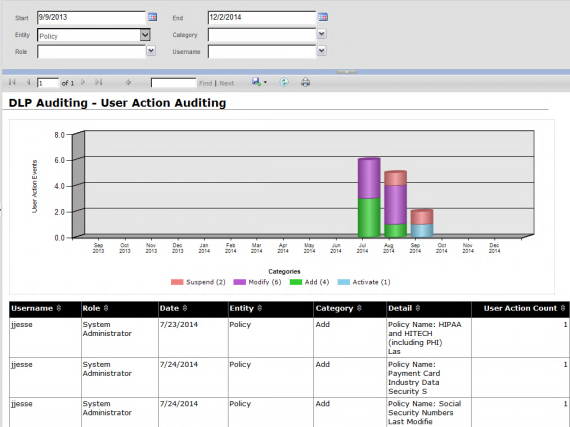
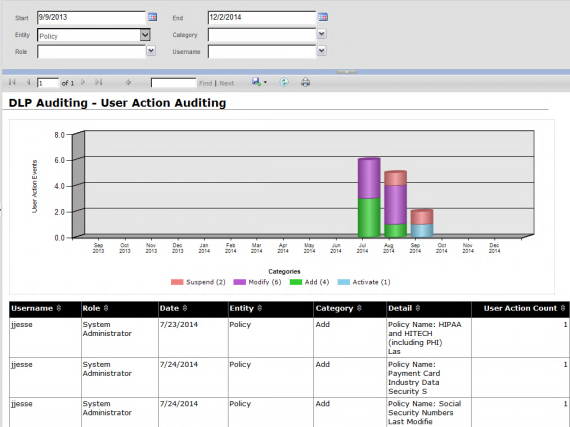
User Action Auditing Report
The first screenshot (User Login Report) shows which users have logged into the DLP system and the second report (User Action Auditing Report) shows who has changed what policies in the DLP system. These two reports are requested over and over by customers. How can I prove to my auditors or management that no one is changing a DLP policy randomly? This information is coming out of the Oracle Database but without ITA you would have to write a SQL statement and then clean it up to provide auditors or management.

Incident Trend By Product Area
A third common request is “how can I show trends” in my DLP system and the above screenshot shows this trend.
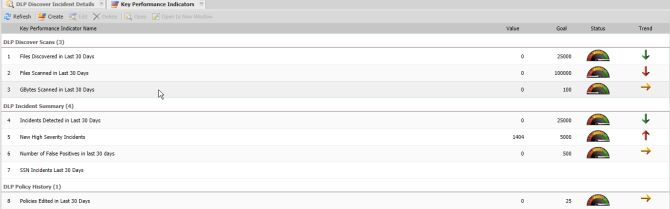
Finally IT Analytics provides Key Performance Indicators (both predefined or custom created) demonstrate how your Symantec DLP system is reducing risk over time and how the system is performing.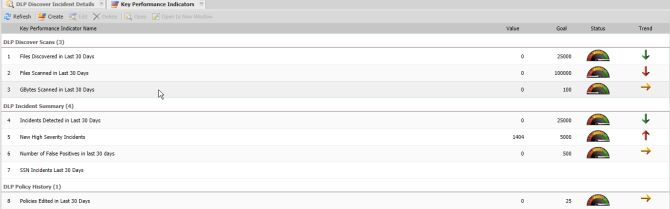
How do I get IT Analytics?
IT Analytics is provided free of charge however a license key and the MSI is needed before you can install ITA.. If you have Symantec Endpoint Protection in your environment the MSI for performing the installation is located on the Tools portion of the media. However if you are not a SEP customer, please contact either your Symantec Account Manager or Bay Dynamics. NOTE: MY company (ITS Partners) can help you obtain the license








You must be logged in to post a comment.